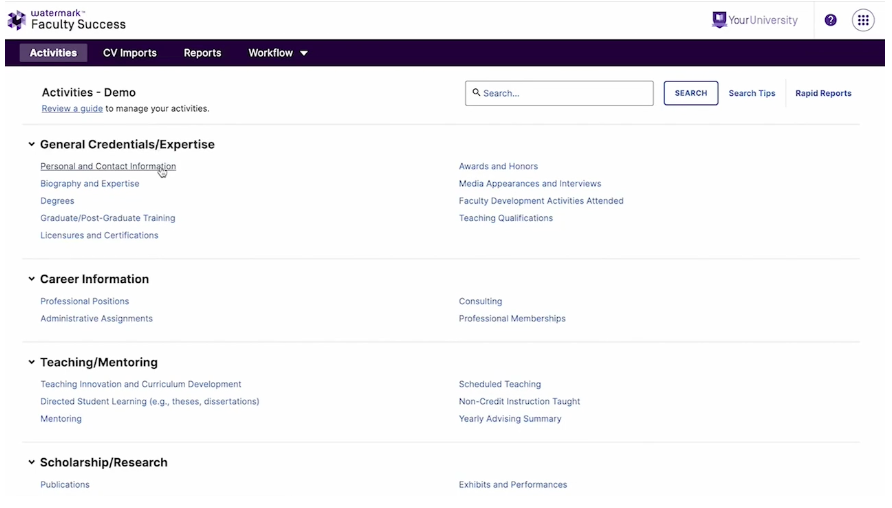
Faculty Success is a central hub for faculty activity data. Get deeper insights into faculty contributions and support their career growth.
institutions use Faculty Success
faculty users
faculty reviews completed annually
accreditation reports run annually
Gather essential information with ease
Did you know that, on average, institutions ask faculty to report on their activities 8 to 12 times a year? This data is essential for accreditation reports and advancing careers, yet traditional systems are tedious and fail to demonstrate the full scope of faculty activity. See what sets Faculty Success apart.
See how Faculty Success is helping clients improve their faculty activity reporting right now. Get in-depth information on topics that matter.
Fill out this form for a live demo, and a member of our team will be in touch with you shortly.